TL;DR: Vulnerability scanners are essential for identifying security risks, but they often come with their own challenges, from false positives to integration headaches. This article dives into troubleshooting common issues, compares top tools like Nessus, Qualys, and Trivy, and provides actionable tips to optimize their performance. Whether you’re a developer or a security engineer, you’ll walk away with practical insights to secure your systems more effectively.
Introduction
Using a vulnerability scanner is a bit like using a smoke detector. When it works well, it alerts you to potential dangers before they become catastrophic. But when it malfunctions—false alarms, missed threats, or constant beeping—it can be more of a headache than a help. The stakes, however, are far higher in cybersecurity. A misconfigured or misunderstood vulnerability scanner can leave your systems exposed or your team drowning in noise.
Vulnerability scanners are indispensable in the modern cybersecurity landscape. They help organizations identify weaknesses in their systems, prioritize remediation efforts, and comply with regulatory requirements. However, their effectiveness depends on proper configuration, regular updates, and integration into broader security workflows. Without these, even the most advanced scanner can fall short.
In this article, we’ll explore the most common issues users face with vulnerability scanners, compare the leading tools in the market, and share best practices for optimizing their performance. Whether you’re using open-source tools like Trivy or enterprise-grade solutions like Nessus and Qualys, this guide will help you troubleshoot effectively and make informed decisions. Additionally, we’ll cover advanced techniques and lesser-known tips to maximize the value of your scanner.
By the end of this guide, you’ll have a deeper understanding of how to navigate the complexities of vulnerability scanning, avoid common pitfalls, and ensure your systems remain secure. Whether you’re a security engineer, developer, or IT administrator, this article is tailored to provide actionable insights.
Common Troubleshooting Scenarios in Vulnerability Scanners
Vulnerability scanners are powerful tools, but they’re not without their quirks. Here are some of the most common issues you’re likely to encounter and how to address them:
1. False Positives
One of the most frustrating aspects of vulnerability scanning is dealing with false positives. These occur when the scanner flags a vulnerability that doesn’t actually exist in your system. False positives can erode trust in the tool and waste valuable time. For example, a scanner might flag a library as vulnerable based on its version number, even if the specific vulnerability has been patched in your environment.
False positives are particularly problematic in large organizations with thousands of assets. Security teams may find themselves overwhelmed by alerts, making it difficult to focus on genuine threats. This can lead to alert fatigue, where critical vulnerabilities are overlooked because they’re buried in a sea of noise.
To address false positives:
- Use the scanner’s built-in suppression or exclusion features to ignore specific findings after validation.
- Keep your scanner’s vulnerability database up to date to reduce outdated or incorrect detections.
- Cross-check findings with secondary tools or manual analysis to confirm their validity.
- Use context-aware scanning options, which allow the scanner to consider environmental factors like compensating controls or mitigations.
{ "vulnerability_id": "CVE-2023-12345", "status": "false_positive", "justification": "Patched in custom build" }⚠️ Security Note: Ignoring false positives without proper validation can lead to overlooking real vulnerabilities. Always verify before dismissing.When dealing with false positives, it’s essential to document your findings and the rationale for marking them as false. This ensures accountability and provides a reference for future audits or investigations.
In some cases, false positives may arise due to outdated scanner signatures or misconfigured rules. Regularly audit your scanner’s configuration and ensure that it aligns with your environment’s unique requirements.
💡 Pro Tip: Collaborate with your development team to understand the context of flagged vulnerabilities. Developers often have insights into custom patches or mitigations that scanners might miss.2. Integration Challenges
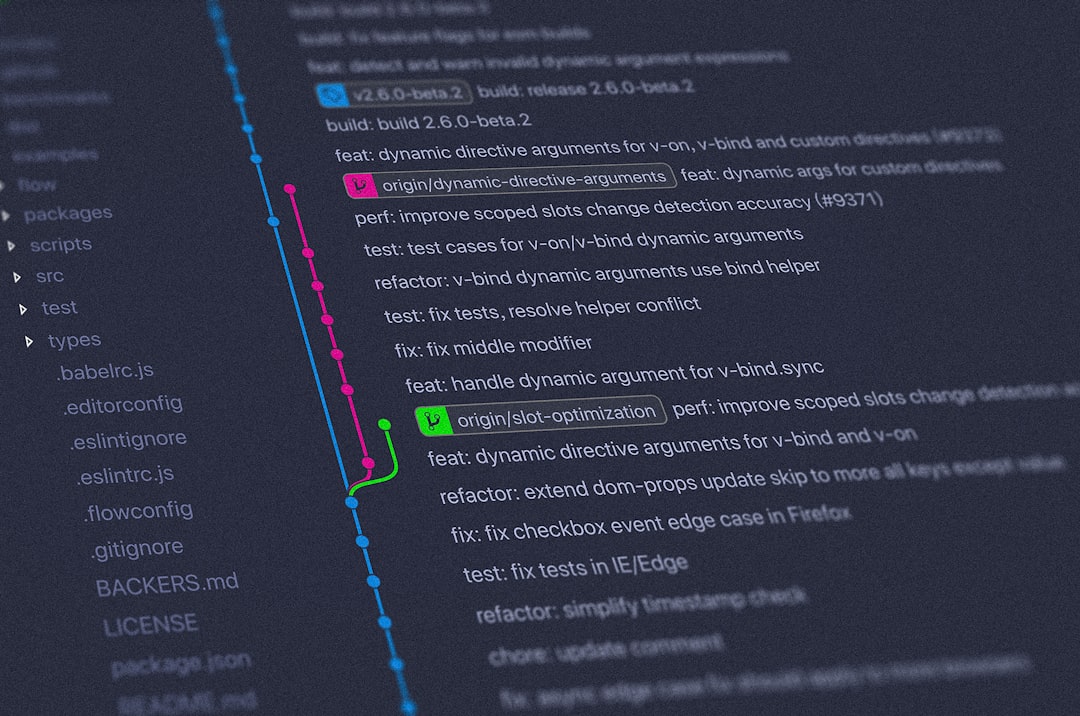
Integrating a vulnerability scanner into your CI/CD pipeline or cloud environment can be tricky. Issues often arise due to mismatched configurations, insufficient permissions, or lack of API support. For example, when integrating Trivy into a Kubernetes cluster, you might encounter permission errors if the scanner doesn’t have the necessary access to your container registry or cluster resources.
Integration challenges can also stem from differences in how tools handle authentication. For instance, Qualys requires API tokens for automation, while Nessus may rely on username-password pairs. Ensuring that these credentials are securely stored and rotated is critical to maintaining a secure integration.
apiVersion: rbac.authorization.k8s.io/v1 kind: Role metadata: name: trivy-scanner rules: - apiGroups: [""] resources: ["pods", "secrets"] verbs: ["get", "list"]Ensure that your scanner has the appropriate RBAC permissions to access the resources it needs. Additionally, test the integration in a staging environment before deploying it to production.
💡 Pro Tip: Use environment-specific configurations to avoid exposing sensitive credentials or permissions in production.For cloud environments, consider using identity and access management (IAM) roles instead of static credentials. This reduces the risk of credential leakage and simplifies access control.
Another common integration challenge involves API rate limits. If your scanner relies heavily on API calls to gather data, ensure that your environment can handle the volume of requests without throttling. Tools like Qualys provide rate-limiting guidelines and best practices for optimizing API usage.
⚠️ Security Note: Avoid hardcoding API keys or credentials in scripts. Use secure vaults or environment variables to store sensitive information.3. Performance Bottlenecks
Scans that take too long can disrupt workflows, especially in CI/CD pipelines. Performance issues are often caused by scanning large files, inefficient configurations, or insufficient resources allocated to the scanner. For example, scanning a monolithic application with hundreds of dependencies can significantly slow down your pipeline.
To mitigate performance bottlenecks:
- Use incremental scanning to focus only on changes since the last scan.
- Exclude unnecessary files or directories from the scan scope.
- Allocate sufficient CPU and memory resources to the scanner, especially in containerized environments.
- Schedule scans during off-peak hours to minimize their impact on production systems.
# Example: Incremental scanning with Trivy
trivy image --ignore-unfixed --skip-update my-app:latestIn addition to these strategies, consider using distributed scanning architectures for large environments. Tools like Qualys support distributed scanning, allowing you to divide the workload across multiple scanners for faster results.
Another approach to improving performance is using caching mechanisms. Some scanners, like Trivy, support caching vulnerability databases locally, which can significantly reduce scan times for recurring scans.
Advanced Comparison Techniques for Vulnerability Scanners
Choosing the right vulnerability scanner isn’t just about picking the most popular tool. It’s about finding the one that aligns with your specific needs. Here’s how to compare them effectively:
1. Coverage
Different scanners excel in different areas. For instance:
- Nessus: Thorough coverage for traditional IT environments, including servers and endpoints.
- Trivy: Specialized in container and Kubernetes security.
- Qualys: Strong in cloud-native and hybrid environments.
When evaluating coverage, consider the types of assets you need to scan. For example, if your organization relies heavily on containerized applications, a tool like Trivy will be more suitable than Nessus. Conversely, if you need to scan legacy systems, Nessus may be a better fit.
Coverage also extends to compliance requirements. If your organization needs to adhere to specific standards like PCI DSS or HIPAA, ensure your scanner supports compliance reporting for those frameworks.
2. Integration
Consider how well the scanner integrates with your existing tools. Does it support your CI/CD pipeline? Can it pull data from your cloud provider? For example, Qualys offers smooth integration with AWS, Azure, and GCP, while Trivy is designed to work natively with Docker and Kubernetes.
Integration isn’t just about compatibility; it’s also about ease of use. Look for tools that provide pre-built plugins or APIs for popular platforms. This can save you time and effort during the setup process.
Some scanners also offer webhook support, enabling real-time notifications for vulnerabilities detected during scans. This can be particularly useful for DevOps teams that need immediate feedback.
{ "webhook_url": "https://example.com/notify", "event": "vulnerability_detected", "severity": "critical" }💡 Pro Tip: Automate vulnerability notifications using webhooks to simplify remediation workflows.3. Usability
A tool is only as good as its usability. Look for features like intuitive dashboards, detailed reporting, and actionable remediation guidance. Nessus, for example, offers a user-friendly interface that simplifies vulnerability management for teams of all sizes.
Usability also extends to the quality of the tool’s documentation and support. A well-documented tool with an active community or responsive support team can make a significant difference in your experience.
For larger teams, consider tools that support role-based access control (RBAC). This allows you to assign specific permissions to team members based on their roles, ensuring secure and efficient collaboration.
💡 Pro Tip: Evaluate the quality of a scanner’s documentation and community forums before committing to it. These resources can be invaluable for troubleshooting.Case Studies: Real-World Troubleshooting Examples
Let’s look at two real-world scenarios where troubleshooting vulnerability scanners made a significant difference:
Case Study 1: False Positives in a Financial Institution
A financial institution using Nessus was overwhelmed by false positives, leading to wasted time and frustration. By tuning the scanner’s sensitivity and using its exclusion features, the team reduced false positives by 40% and regained confidence in their vulnerability management process.
Additionally, the institution implemented a secondary validation process using manual checks and cross-referencing with other tools like Qualys. This ensured that critical vulnerabilities were not overlooked.
Case Study 2: Integration Issues in a DevOps Environment
A DevOps team struggled to integrate Trivy into their Jenkins pipeline due to permission errors. By updating their RBAC configurations and using Trivy’s CLI options, they resolved the issue and achieved smooth integration.
The team also used Trivy’s caching feature to reduce scan times, enabling faster feedback loops in their CI/CD pipeline.
Feature Comparison Chart: Beyond the Basics
Here’s a quick comparison of some of the top vulnerability scanners:
| Feature | Nessus | Trivy | Qualys |
|---|---|---|---|
| Focus Area | IT Infrastructure | Containers & Kubernetes | Cloud & Hybrid Environments |
| Integration | Limited CI/CD | Excellent for CI/CD | Strong Cloud Integration |
| Pricing | Paid | Free & Paid | Paid |
| Compliance Reporting | Yes | Limited | Yes |
Best Practices for Optimizing Vulnerability Scanner Performance
To get the most out of your vulnerability scanner, follow these best practices:
- Regular Updates: Keep your scanner and its vulnerability database up to date.
- Incremental Scanning: Focus on changes rather than scanning everything from scratch.
- Automation: Integrate your scanner into your CI/CD pipeline for continuous monitoring.
- Validation: Always validate findings to avoid acting on false positives.
- Documentation: Maintain detailed records of scan results, exclusions, and remediation efforts.
Another best practice is to conduct periodic audits of your scanner’s configuration. This ensures that the tool remains aligned with your organization’s evolving security needs.
Frequently Asked Questions
What is the best vulnerability scanner for containers?
Trivy is an excellent choice for containerized applications due to its lightweight design and smooth Kubernetes integration.
How can I reduce false positives?
Use exclusion features, validate findings, and keep your scanner’s database updated to minimize false positives.
Can vulnerability scanners integrate with CI/CD pipelines?
Yes, tools like Trivy and Qualys offer resilient CI/CD integration options for automated scanning.
Are free vulnerability scanners reliable?
Free scanners like Trivy are reliable for specific use cases, but enterprise environments may require paid solutions for thorough coverage.
Tools and books mentioned in (or relevant to) this article:
- Zero Trust Networks — Building secure systems in untrusted networks ($40-50)
- The Web Application Hacker’s Handbook — Finding and exploiting security flaws in web applications ($35-45)
- Threat Modeling: Designing for Security — Systematic approach to finding and addressing threats in software ($35-45)
- YubiKey 5 NFC — Hardware security key for SSH, GPG, and MFA ($45-55)
Conclusion
Here’s what to remember:
- Choose a scanner that aligns with your specific needs (e.g., Nessus for IT, Trivy for containers).
- Address common issues like false positives and integration challenges proactively.
- Optimize performance with regular updates, incremental scanning, and automation.
Have a favorite vulnerability scanner or a troubleshooting tip? Share your thoughts in the comments or reach out on Twitter. Next time, we’ll explore how to secure your CI/CD pipeline end-to-end.