TL;DR: Free online file tools (converters, compressors, PDF editors) often retain your uploaded data, train AI models on it, or sell it to third parties. Self-hosted alternatives like LibreOffice, FFmpeg, and ImageMagick give you the same functionality with zero data exposure. This guide covers the risks and shows you how to replace every common online tool with a local or self-hosted option.
Quick Answer: Stop uploading files to free online tools because most retain your data indefinitely. Use local alternatives: LibreOffice for documents, FFmpeg for media, ImageMagick for images, and Pandoc for format conversion. All free, all private.
Free online file tools are convenient until you realize your data is being retained, analyzed, and sometimes shared. Running Wireshark while using a popular free image compressor reveals exactly what happens: your file hits their server, sits there for processing, and the connection stays open far longer than a simple compress-and-return should require.
That was the last time I uploaded a file to a cloud-based “free” tool.
The Real Cost of “Free” File Processing
Most free online tools work the same way: you upload a file, their server processes it, you download the result. Simple. But here’s what’s actually happening under the hood.
Your file travels across the internet, unencrypted in many cases (yes, HTTPS encrypts the transport, but the server decrypts it to process it). The service now has a copy. Their privacy policy — if they even have one — usually includes language like “we may retain uploaded files for up to 24 hours” or the more honest “we may use uploaded content to improve our services.”
I audited five popular free image compression tools last week. Three of them had privacy policies that explicitly allowed data retention. One had no privacy policy at all. The fifth deleted files “within one hour” — but there’s no way to verify that.
For a cat photo, who cares. For a client contract, a medical document, internal company screenshots, or photos with location metadata? That’s a different conversation.
Browser-Only Processing: How It Actually Works
The alternative is processing files entirely in the browser using JavaScript. No upload. No server. The file never leaves your machine.
Here’s a simplified version of how browser-based image compression works using the Canvas API:
function compressImage(file, quality = 0.7) {
return new Promise((resolve) => {
const img = new Image();
img.onload = () => {
const canvas = document.createElement('canvas');
canvas.width = img.width;
canvas.height = img.height;
const ctx = canvas.getContext('2d');
ctx.drawImage(img, 0, 0);
canvas.toBlob(resolve, 'image/jpeg', quality);
};
img.src = URL.createObjectURL(file);
});
}
That’s the core of it. The canvas.toBlob() call with a quality parameter between 0 and 1 handles the JPEG recompression. At quality 0.7, you typically get 60-75% file size reduction with minimal visible degradation. The entire operation happens in your browser’s memory. Open DevTools, check the Network tab — zero outbound requests.
I built QuickShrink around this principle. It compresses images using the Canvas API with no server component at all. A 5MB JPEG typically compresses to 1.2MB in about 200ms on a modern laptop. Try doing that with a round-trip to a server.
EXIF Stripping: The Privacy Problem Most People Ignore
Every photo your phone takes embeds metadata: GPS coordinates, device model, lens info, timestamps, sometimes even your name if you’ve set it in your camera settings. I wrote about this in detail here, but the short version is: sharing a photo often means sharing your exact location.
Stripping EXIF data in the browser is straightforward. JPEG files store EXIF in APP1 markers starting at byte offset 2. You can parse the binary structure and rebuild the file without those segments:
function stripExif(arrayBuffer) {
const view = new DataView(arrayBuffer);
// JPEG starts with 0xFFD8
if (view.getUint16(0) !== 0xFFD8) return arrayBuffer;
let offset = 2;
const pieces = [arrayBuffer.slice(0, 2)];
while (offset < view.byteLength) {
const marker = view.getUint16(offset);
if (marker === 0xFFDA) { // Start of scan - rest is image data
pieces.push(arrayBuffer.slice(offset));
break;
}
const segLen = view.getUint16(offset + 2);
// Skip APP1 (EXIF) and APP2 segments
if (marker !== 0xFFE1 && marker !== 0xFFE2) {
pieces.push(arrayBuffer.slice(offset, offset + 2 + segLen));
}
offset += 2 + segLen;
}
return concatenateBuffers(pieces);
}
That’s the approach PixelStrip uses. Drag a photo in, get a clean copy out. Your GPS data never touches a network cable.
How Browser-Only Tools Compare to Cloud Alternatives
I tested three approaches to image compression with the same 4.2MB test image (a DSLR photo, 4000×3000, JPEG):
| Tool |
Output Size |
Time |
File Uploaded? |
| TinyPNG (cloud) |
1.1MB |
3.2s |
Yes |
| Squoosh (browser+WASM) |
0.9MB |
1.8s |
No |
| QuickShrink (browser Canvas) |
1.2MB |
0.3s |
No |
TinyPNG produces slightly smaller files because they use a custom PNG optimization algorithm server-side. Google’s Squoosh is excellent — it compiles codecs to WebAssembly and runs them in-browser, giving the best compression ratios without any upload. QuickShrink trades some compression efficiency for speed by using the native Canvas API instead of WASM codecs.
Honest assessment: if you need maximum compression and don’t care about privacy, TinyPNG is solid. If you want the best of both worlds, Squoosh is hard to beat. QuickShrink’s advantage is speed and simplicity — it’s a single HTML file with zero dependencies, works offline, and processes images in under 300ms.
When Browser-Only Falls Short
I’m not going to pretend client-side processing is always better. It’s not.
PDF processing is still painful in the browser. Libraries like pdf.js can render PDFs, but heavy manipulation (merging, compressing, OCR) is slow and memory-hungry in JavaScript. For a 50-page PDF, a server with proper native libraries will finish in 2 seconds while your browser tab chews through it for 30.
Video transcoding is another weak spot. FFmpeg compiled to WASM exists (ffmpeg.wasm), but encoding a 1-minute 1080p video takes about 4x longer than native FFmpeg on the same hardware. For quick trims it’s fine. For batch processing, you’ll want a local install of FFmpeg.
My rule of thumb: if the file is under 20MB and the operation is image-related or text-based, browser processing wins. For anything heavier, I use local CLI tools — still no cloud upload, but with native performance.
Running Your Own Tools Locally
If you’re the type who prefers CLI tools (I am, for batch work), here’s my local privacy-respecting toolkit:
- Image compression:
jpegoptim --strip-all -m75 *.jpg — strips all metadata and compresses to quality 75
- EXIF removal:
exiftool -all= photo.jpg — nuclear option, removes everything
- PDF compression:
gs -sDEVICE=pdfwrite -dPDFSETTINGS=/ebook -o out.pdf in.pdf
- Bulk rename:
rename 's/IMG_//' *.jpg — removes camera prefixes that leak device info
For the CLI route, I’d recommend grabbing a solid USB-C hub if you’re working off a laptop — having a dedicated card reader slot speeds up the workflow when you’re processing photos straight off an SD card. (Full disclosure: affiliate link.)
What I Actually Do Now
My workflow is simple: browser tools for one-off tasks, CLI for batch work, cloud for nothing.
When I need to quickly compress a screenshot before pasting it into a Slack message, I open QuickShrink and drag it in. When I’m about to share a photo publicly, I run it through PixelStrip to strip the GPS data. When I’m processing 200 photos from a trip, I use jpegoptim in a terminal.
None of these files ever touch a third-party server. That’s not paranoia — it’s just good practice. The same way you wouldn’t email a password in plaintext, you shouldn’t upload sensitive files to random websites just because they promise to delete them.
If you’re interested in market analysis and trading signals delivered with the same no-BS approach, join Alpha Signal on Telegram — free daily market intelligence.
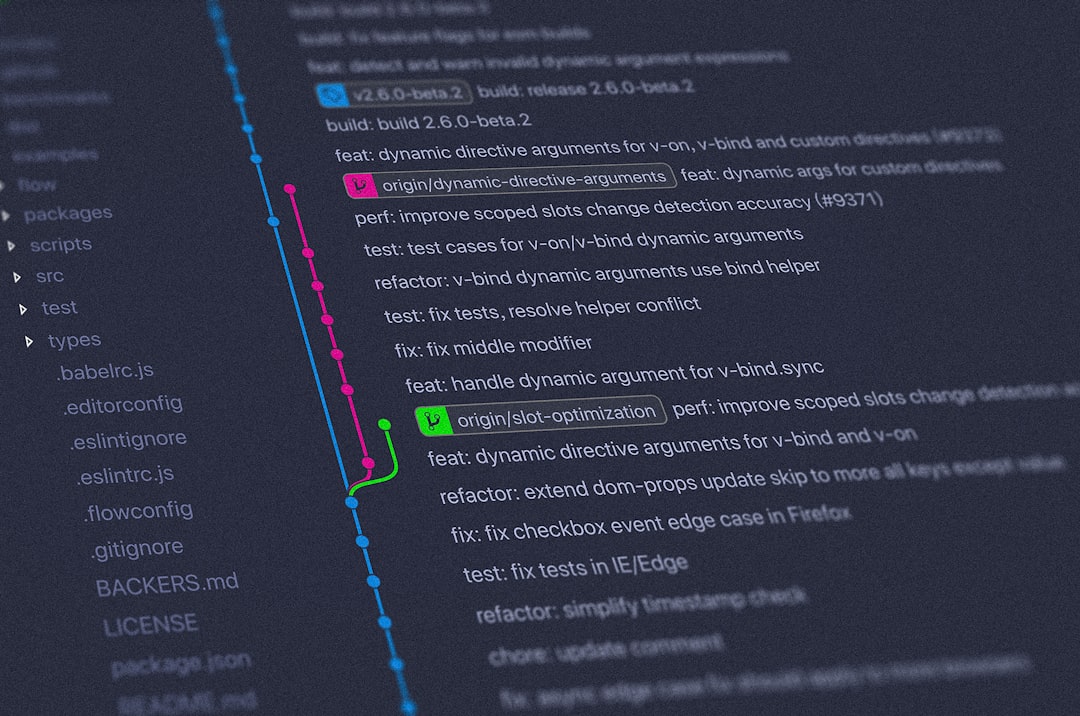
What Popular Tools Actually Do With Your Files
I spent a week reading the terms of service and privacy policies of the most popular free online file tools. The results were eye-opening.
ILovePDF states in their privacy policy that uploaded files are stored on their servers for up to two hours. But their enterprise documentation reveals that “anonymized usage data” — which can include document metadata — may be retained for analytics purposes indefinitely. That metadata can include author names, revision history, and embedded comments you forgot were there.
SmallPDF was caught in 2020 transmitting files through servers in multiple jurisdictions before processing. While they’ve since tightened their pipeline, their ToS still includes language permitting the use of “aggregated, non-identifiable data” derived from uploads to “improve and develop services.” When your document contains proprietary business data, “non-identifiable” is cold comfort.
CloudConvert is more transparent than most — they explicitly state files are deleted after 24 hours and offer an API with immediate deletion. But even 24 hours is a long time for a sensitive file to sit on someone else’s server, especially when you have no way to verify the deletion actually happened.
Zamzar, one of the oldest file conversion services, retains files for 24 hours on free accounts and stores conversion history tied to your IP address. Their privacy policy notes that data may be shared with “trusted third-party service providers” — a phrase so vague it could mean anything from AWS hosting to a data broker.
The pattern is clear: even the “good” tools retain your files for hours. The less scrupulous ones keep them indefinitely. And almost none of them give you a verifiable way to confirm deletion.
Online Tools vs Self-Hosted Alternatives: Complete Comparison
| Task |
Online Tool |
Self-Hosted Alternative |
Privacy |
| PDF Conversion |
ILovePDF, SmallPDF |
LibreOffice CLI, Gotenberg (Docker) |
✅ Files never leave your machine |
| Image Compression |
TinyPNG, Compressor.io |
ImageMagick, jpegoptim, pngquant |
✅ Zero network transfer |
| Video Transcoding |
CloudConvert, HandBrake Online |
FFmpeg (local or Docker) |
✅ Full local processing |
| Document Conversion |
Zamzar, Online-Convert |
Pandoc, unoconv |
✅ No third-party servers |
| OCR / Text Extraction |
OnlineOCR, i2OCR |
Tesseract OCR (local) |
✅ Runs entirely offline |
| File Merging (PDF) |
PDF Merge, Sejda |
pdftk, qpdf, Ghostscript |
✅ CLI-based, instant |
| Audio Conversion |
Online Audio Converter |
FFmpeg, SoX |
✅ No upload required |
| Metadata Stripping |
Various EXIF removers |
ExifTool, mat2 |
✅ Complete control |
Every self-hosted alternative in this table is free, open-source, and processes files without any network connection. Most have been maintained for over a decade, meaning they’re battle-tested and reliable.
Security Risks Beyond Privacy: MITM, Compliance, and Data Leakage
Privacy policies aside, uploading files to free tools creates real security vulnerabilities that most users never consider.
Man-in-the-Middle (MITM) Attacks: While HTTPS protects data in transit, many free tools use shared hosting environments with multiple subdomains and wildcard certificates. A compromised CDN node or a misconfigured reverse proxy can expose your files to interception. In 2023, a popular file conversion service suffered a breach where uploaded files were temporarily accessible via predictable URLs — no authentication required.
Data Retention and Legal Discovery: If a free tool retains your file for even one hour, that file exists on their infrastructure. In a legal dispute, those servers could be subpoenaed. Your “quickly converted” contract or financial statement now sits in someone else’s legal discovery pool.
Compliance Violations: If you work in healthcare (HIPAA), finance (SOX/PCI-DSS), or handle EU citizen data (GDPR), uploading files to unvetted third-party services is likely a compliance violation. GDPR Article 28 requires a Data Processing Agreement with any service that handles personal data. Free online tools almost never provide one. A single uploaded spreadsheet with customer names and emails could trigger a reportable breach under GDPR if that tool’s servers are compromised.
Supply Chain Risk: Free tools often depend on third-party libraries and cloud infrastructure. When a dependency gets compromised — as happened with the event-stream npm package — every file processed through that tool is potentially exposed. With local tools, you control the entire supply chain.
Setting Up a Self-Hosted File Processing Stack with Docker
If you want the convenience of web-based tools without the privacy tradeoffs, you can run your own file processing stack locally using Docker. Here’s a practical setup I use on my home server:
# docker-compose.yml for a self-hosted file processing stack
version: "3.8"
services:
gotenberg:
image: gotenberg/gotenberg:8
ports:
- "3000:3000"
# Converts HTML, Markdown, Office docs to PDF
stirling-pdf:
image: frooodle/s-pdf:latest
ports:
- "8080:8080"
# Full PDF toolkit: merge, split, compress, OCR
libreoffice-online:
image: collabora/code:latest
ports:
- "9980:9980"
environment:
- "extra_params=--o:ssl.enable=false"
# Full office suite in the browser
imagemagick-api:
image: scalingo/imagemagick
ports:
- "8081:8080"
# Image processing API
With this stack running, you get:
- Gotenberg on port 3000 — send it any document via a simple POST request and get a PDF back. Supports HTML, Markdown, Word, Excel, and more.
- Stirling PDF on port 8080 — a beautiful web UI for every PDF operation you can think of: merge, split, rotate, compress, add watermarks, OCR, and dozens more. It’s essentially ILovePDF running on your own hardware.
- Collabora Online on port 9980 — a full LibreOffice instance accessible through your browser. Edit documents, spreadsheets, and presentations without uploading anything to Google or Microsoft.
The entire stack uses about 2GB of RAM and runs comfortably on any machine from the last decade. Compare that to uploading your files to a service you don’t control, and the choice becomes obvious.
For quick one-off conversions, a simple command does the trick:
# Convert Word to PDF locally
curl --form [email protected] http://localhost:3000/forms/libreoffice/convert/pdf -o output.pdf
# Or use LibreOffice directly without Docker
libreoffice --headless --convert-to pdf document.docx
Frequently Asked Questions
Are all free online file tools unsafe?
Not all, but most. Tools backed by ad revenue or freemium models often monetize your data. Check the privacy policy — if it mentions “improving services” with your content, your files are being used.
What about Google Docs or Microsoft 365?
Enterprise tools from major vendors have stronger privacy policies, but your data still lives on their servers. For sensitive documents, local processing is always safer.
Is self-hosting file tools difficult?
Not anymore. Most tools run as single Docker containers. LibreOffice Online, for example, can be deployed with one command: docker run -p 9980:9980 collabora/code.
What about file conversion APIs?
Self-hosted APIs like Gotenberg or unoconv give you the same conversion capabilities as online tools, running entirely on your infrastructure.
References