Why Pre-IPO Valuation Tracking Matters in 2026 📌 TL;DR: Why Pre-IPO Valuation Tracking Matters in 2026 The private tech market has exploded. SpaceX is now valued at over $2 trillion by public markets, OpenAI at $1.3 trillion, and the total implied market cap of the top 21 pre-IPO companies exceeds $7… Read more →
Security, DevOps & Trading Tech — Practical Guides
-
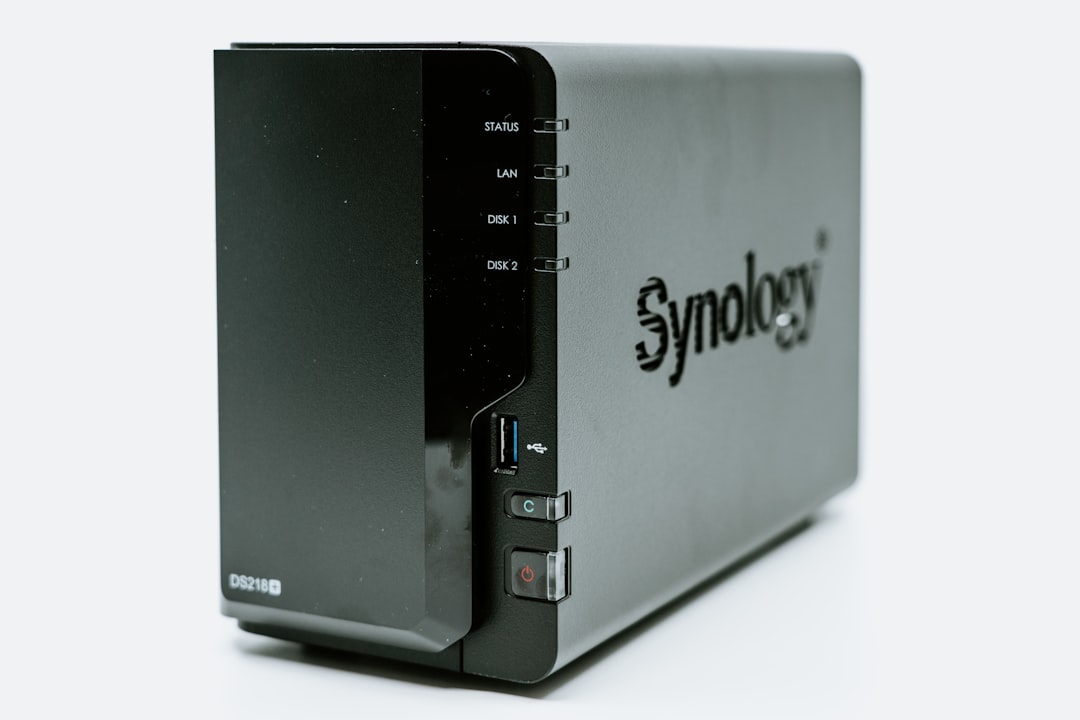
Best Drives for TrueNAS 2026: HDDs, SSDs & My Setup
SMART warnings are the canary you ignore until a drive dies mid-rebuild. Choosing the right drives for TrueNAS in 2026 means navigating the HDD-vs-SSD transition, understanding CMR vs SMR write penalties, and accepting that consumer drives in a ZFS mirror are a calculated risk. That rebuild forced me to actually research… Read more →
-
CVE-2026-20131: Cisco FMC Zero-Day Exploited by Ransomware
I triaged CVE-2026-20131 for my own network the day it dropped. If you run Cisco FMC anywhere in your environment, this is a stop-what-you’re-doing moment. A critical zero-day vulnerability in Cisco Secure Firewall Management Center (FMC) has been actively exploited by the Interlock ransomware group since January 2026 — more than… Read more →
-
Claude Code Leak: npm Security, TypeScript, AI Architecture
When source maps for a major AI coding tool leaked via an npm package, I spent a week analyzing what was exposed and how it happened. The leak revealed internal architecture, agent orchestration patterns, and TypeScript code that was never meant to be public. This isn’t theoretical — it’s a… Read more →
-

Securing Kubernetes Supply Chains with SBOM & Sigstore
After implementing SBOM signing and verification across 50+ microservices in production, I can tell you: supply chain security is one of those things that feels like overkill until you find a compromised base image in your pipeline. Here’s what actually works in practice — not theory, but the exact patterns… Read more →
-

Self-Host Ollama: Local LLM Inference on Your Homelab
The $300/Month Problem 📌 TL;DR: The $300/Month Problem I hit my OpenAI API billing dashboard last month and stared at $312.47. That’s what three months of prototyping a RAG pipeline cost me — and most of those tokens were wasted on testing prompts that didn’t work. 🎯 Quick Answer: Self-hosting Ollama on… Read more →
-
Backup & Recovery: Enterprise Security for Homelabs
Learn how to apply enterprise-grade backup and disaster recovery practices to secure your homelab and protect critical data from unexpected failures. Why Backup and Disaster Recovery Matter for Homelabs 📌 TL;DR: Learn how to apply enterprise-grade backup and disaster recovery practices to secure your homelab and protect critical data from unexpected failures…. Read more →
-
Penetration Testing Basics for Developers
I started doing penetration testing because I got tired of finding the same vulnerabilities in code reviews. Once you learn to think like an attacker, you write fundamentally different code. I run regular pen tests against my own homelab services — it’s the fastest way to internalize security. Here’s how… Read more →
-
Terraform Security: Encryption, IAM & Drift Detection
What happens when your Terraform state file ends up in the wrong hands? Spoiler: it’s not pretty, and your cloud environment might as well send out party invitations to every hacker on the internet. Keeping your Terraform setup secure can feel like trying to lock the front door while someone’s already… Read more →